Tags
bugbounty
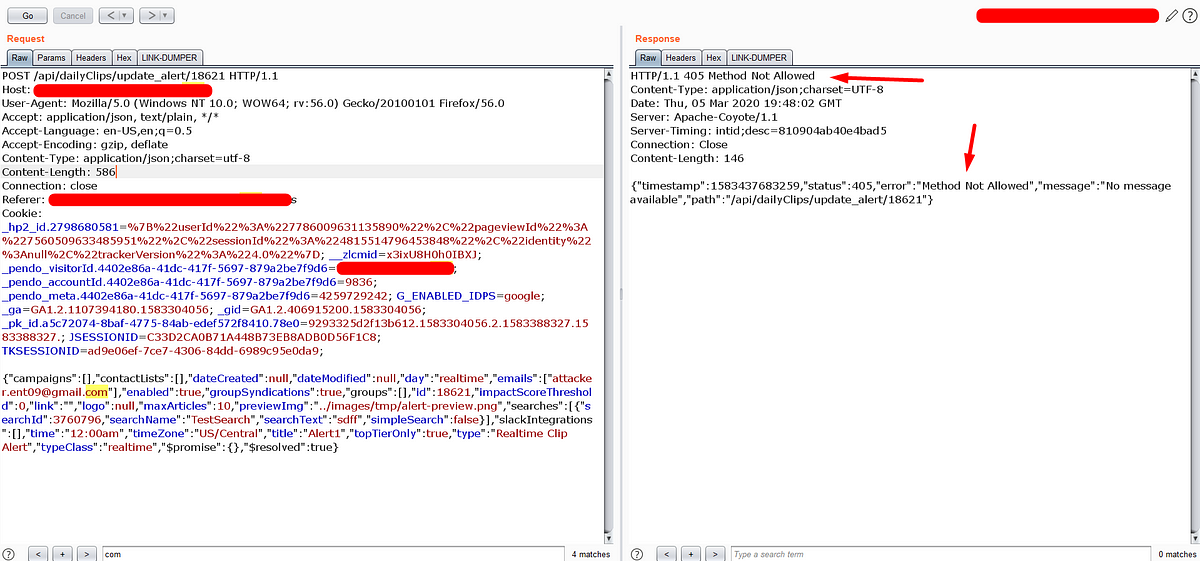
How I perform the JSON CSRF with method override technique.
CSRF(Cross-Site Request Forgery) is a kind of web application vulnerability, using this a malevolent can forge the HTTP request without the actual user knowledge. This will result in ...
In WebSecurity, APISecurity, Dec 29, 2023Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
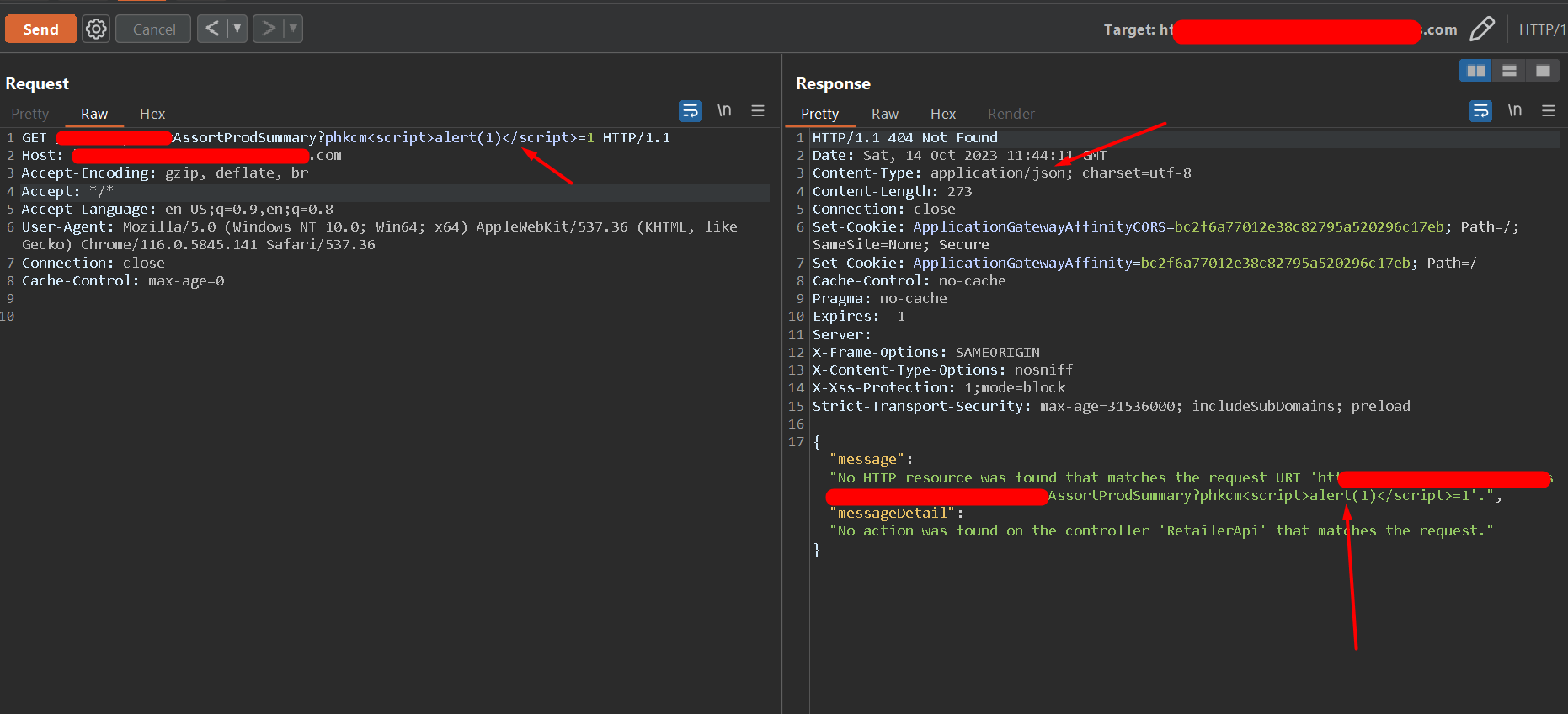
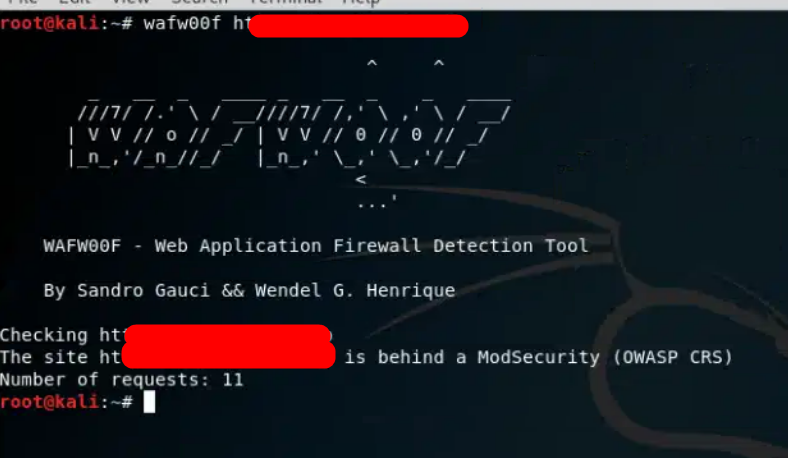
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
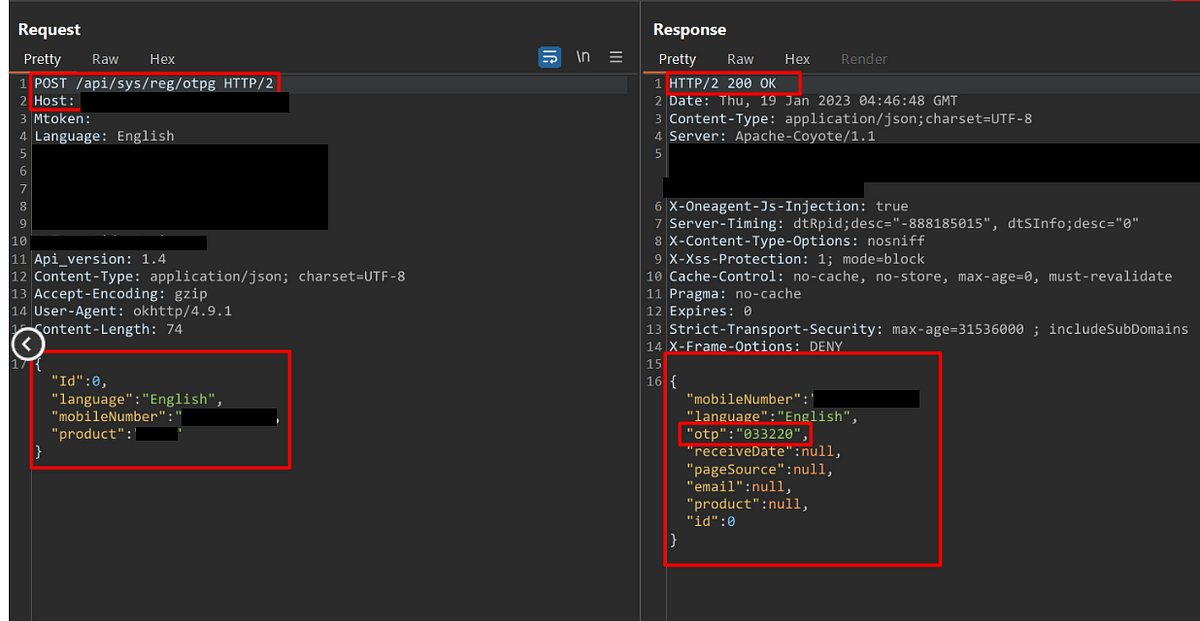
In WebSecurity, cross-site-scripting, Sep 30, 2023Learn and Earn with the Most Common Unsecured Methods of OTP Bypass Techniques.
Discover the ultimate guide for bug bounty hunters to detect sneaky OTP validation vulnerabilities!
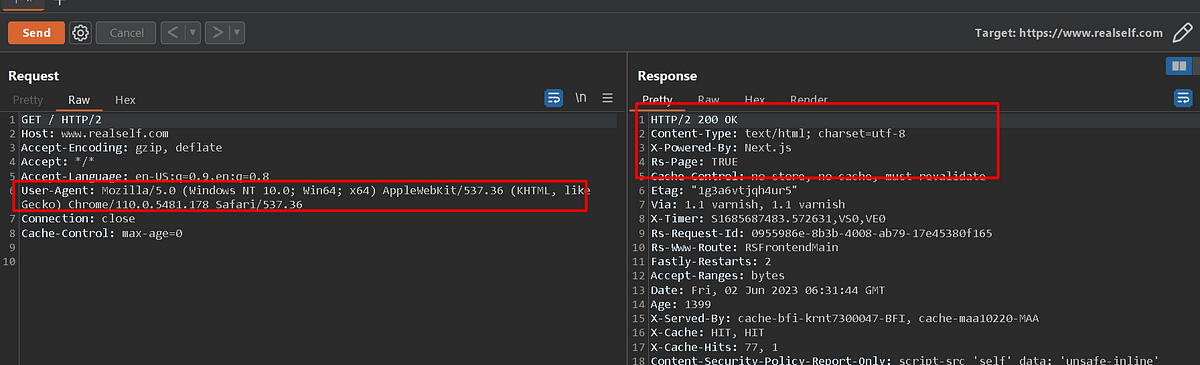
In WebSecurity, APISecurity, Jul 11, 2023The Importance of Checking User-Agent Header Dependency in Penetration Testing.
Never ever give a chance to leave a bug to automated scanners.Introduction:
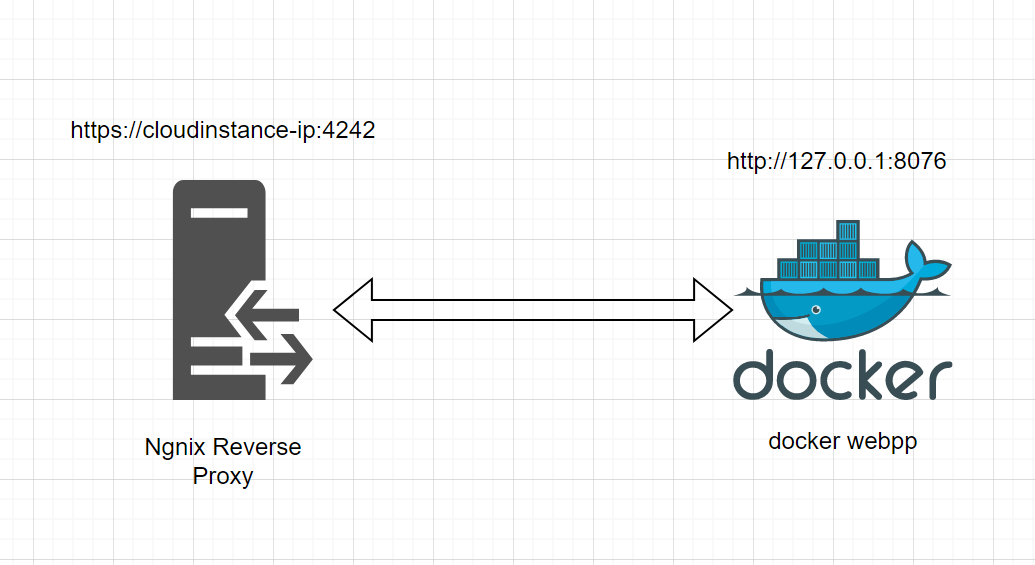
In WebSecurity, APISecurity, Jun 02, 2023How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022Never leave this tip while you are hunting Broken Access Control.
A special Bug-Bounty tip for Bug hunters and Pen-testers
In WebSecurity, APISecurity, Nov 12, 2021How-to-deploy-a-personal-VPN-in-Linode
A better way to take control of your online privacy
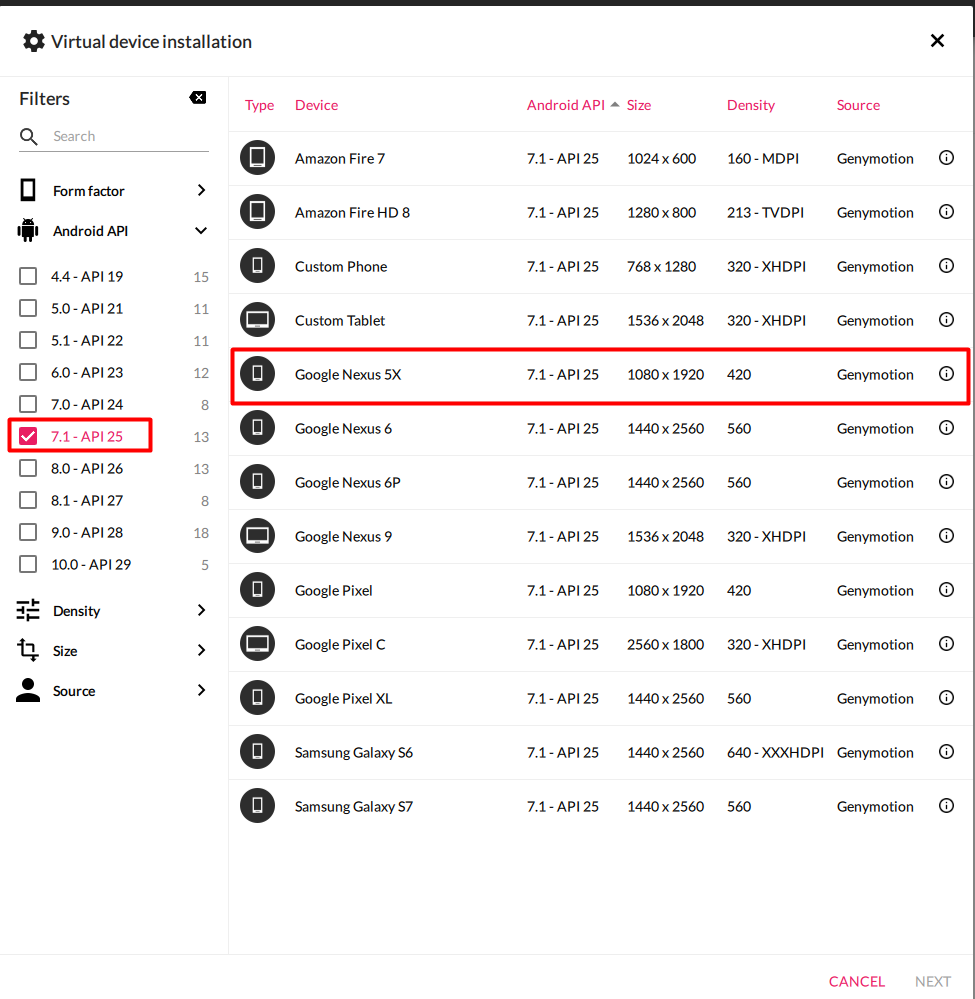
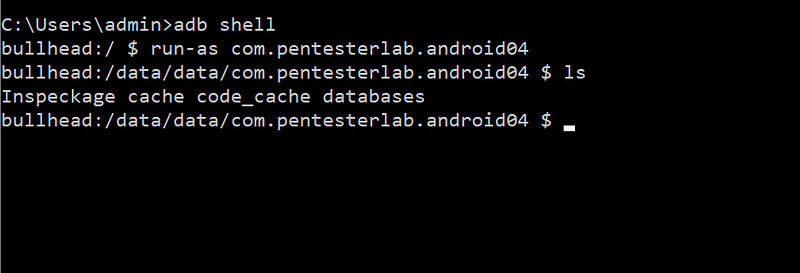
In secureinfrastructure, Jul 11, 2021Genymotion-Xposed-Inspeckage-Setup.
Android application dynamic analysis lab setup on windows
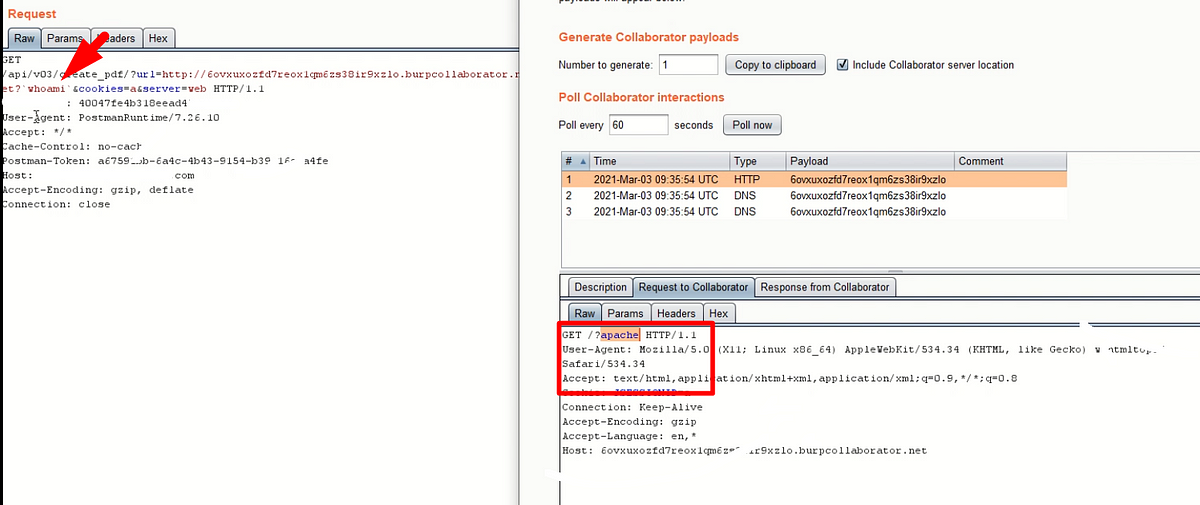
In AndroidSecurity, MobileAppPT, Jul 03, 2021An unknown Linux secret that turned SSRF to OS Command injection.
A weird approach to escalate the Server-Side Request Forgery
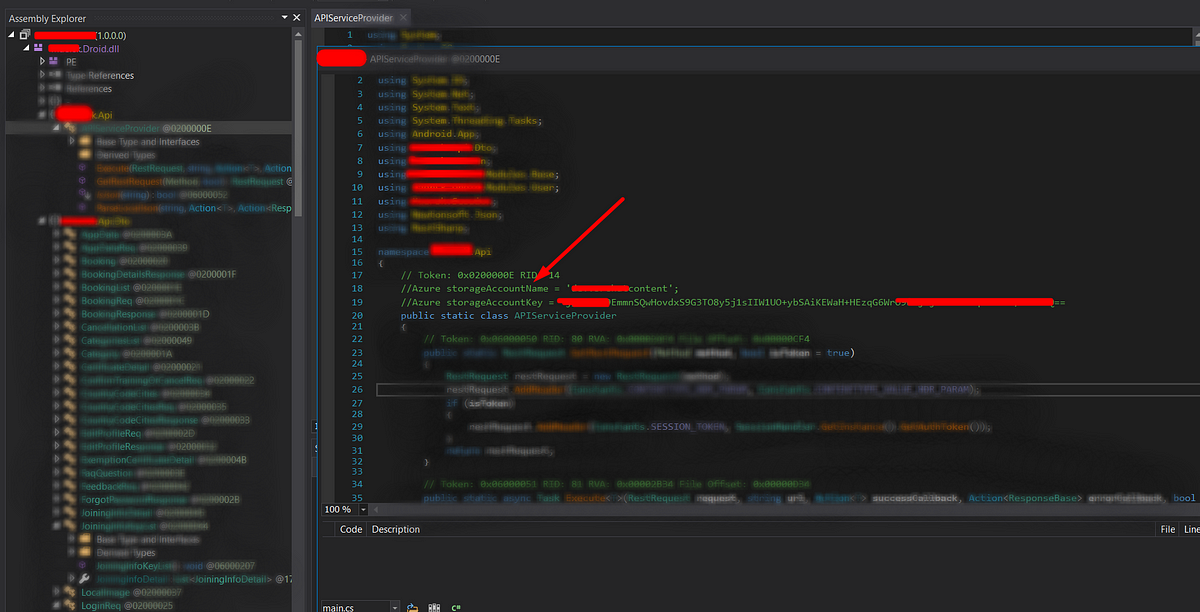
In WebSecurity, APISecurity, Mar 17, 2021Let’s know How I have explored the buried secrets in the Xamarin application.
Mobile Application Penetration Testing Guide
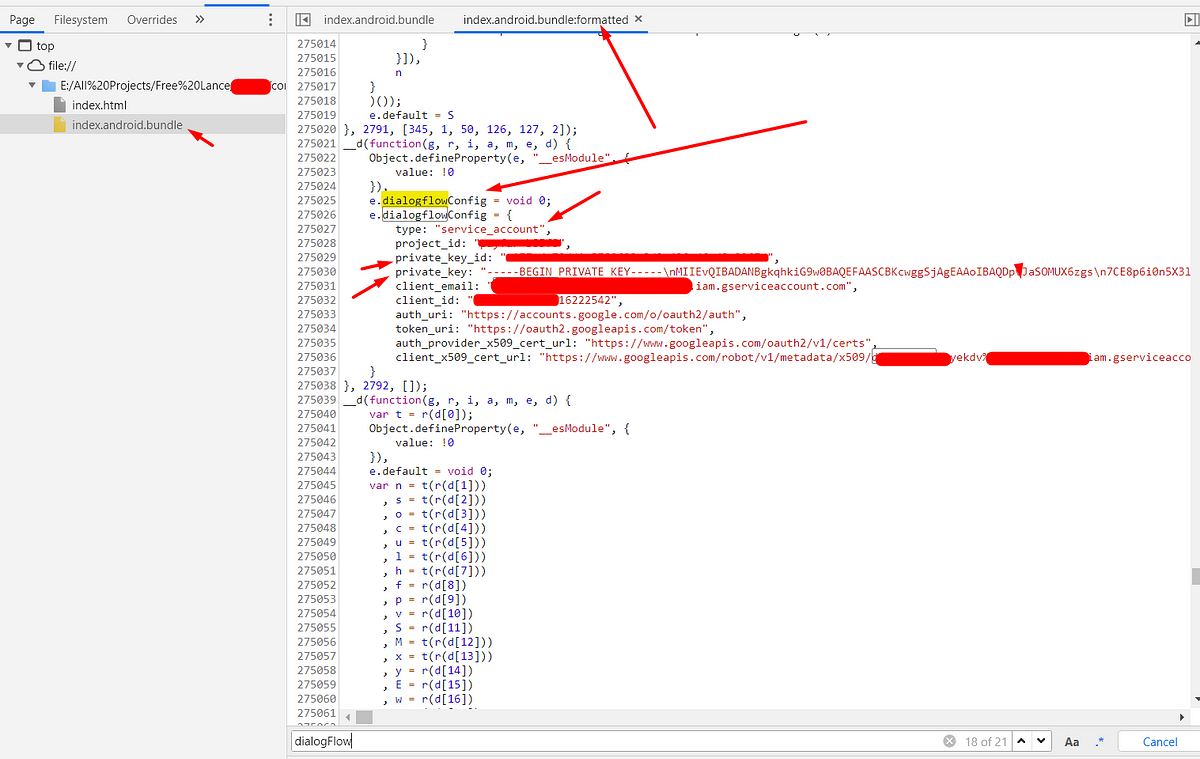
In AndroidSecurity, MobileAppPT, Feb 20, 2021Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
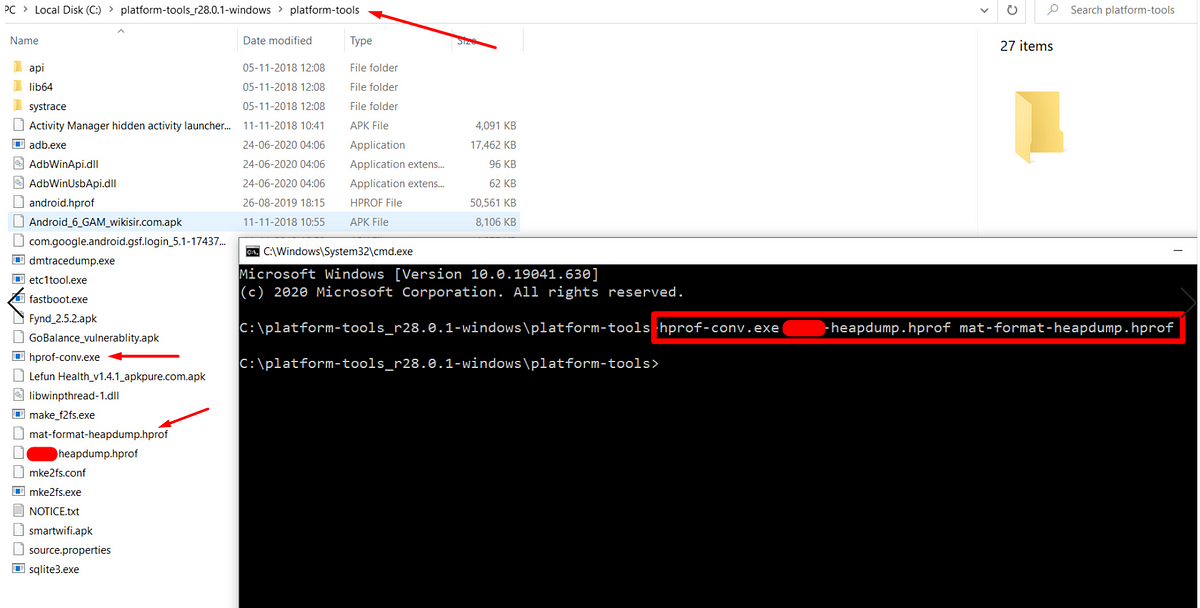
In AndroidSecurity, MobileAppPT, Jan 18, 2021Hack crypto secrets from heap memory to exploit Android application.
Due to the short time of development, The developers only focus on the building feature, functionalities and UI components. But they may…
In AndroidSecurity, MobileAppPT, Dec 22, 2020Android Hacking Fundamentals -Part-2.
By defalut production build of Android (that’s what you have on your phone until you unlock the bootloader and flash the phone with …
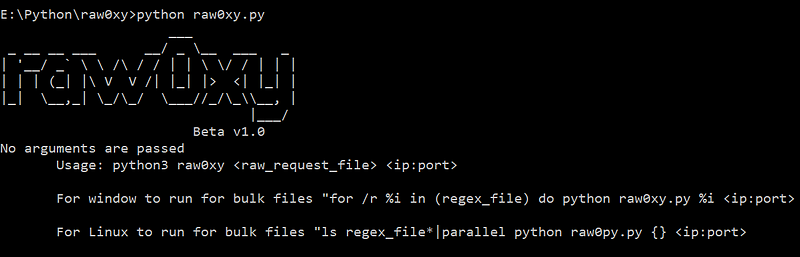
In MobileAppPT, AndroidSecurity, Dec 18, 2020Let’s pen-test make easier with raw0xy.
raw0xy is a python script, takes a file that contains raw HTTP request and a proxy route. Then the script will parse the raw HTTP request…
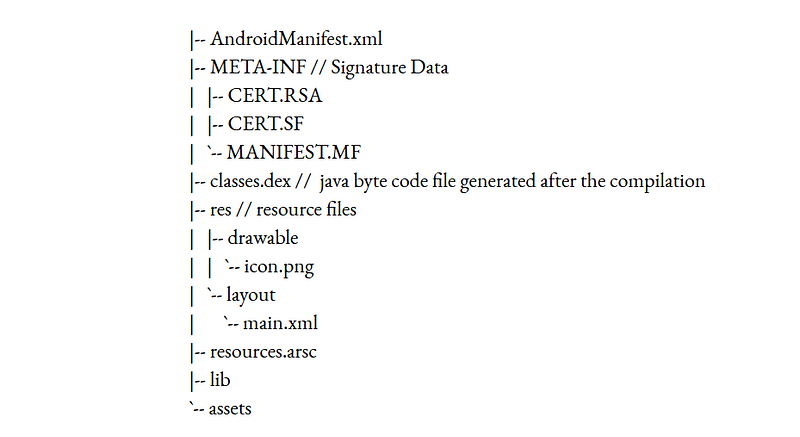
In WebSecurity, APISecurity, Dec 16, 2020Android Hacking Fundamentals -Part-1.
Before learning about the android application hacking, it is necessary to understand the fundamental concepts of android application files, components and how the different components...
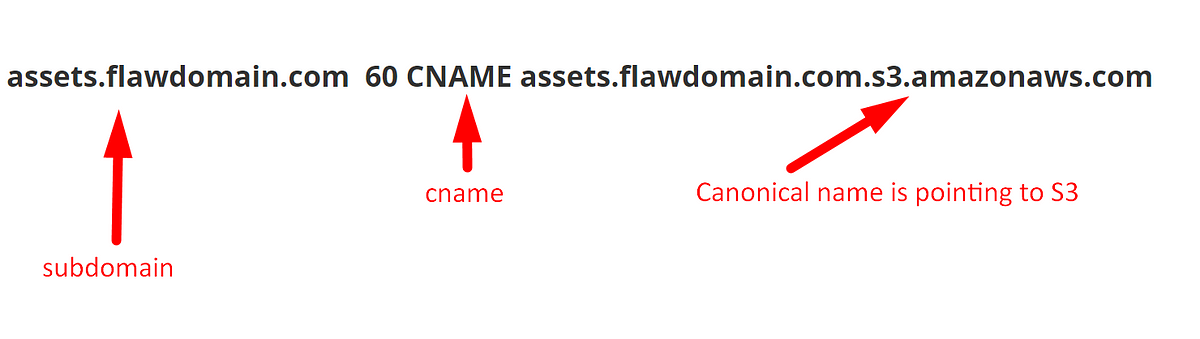
In AndroidSecurity, MobileAppPT, Sep 27, 2020Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020Every Bug Bounty hunter should know the evil smile of the JSONP over the browser’s Same Origin.
JSONP stands for JSON with Padding. It is a JavaScript technique to request the data from the server and can access without worrying about
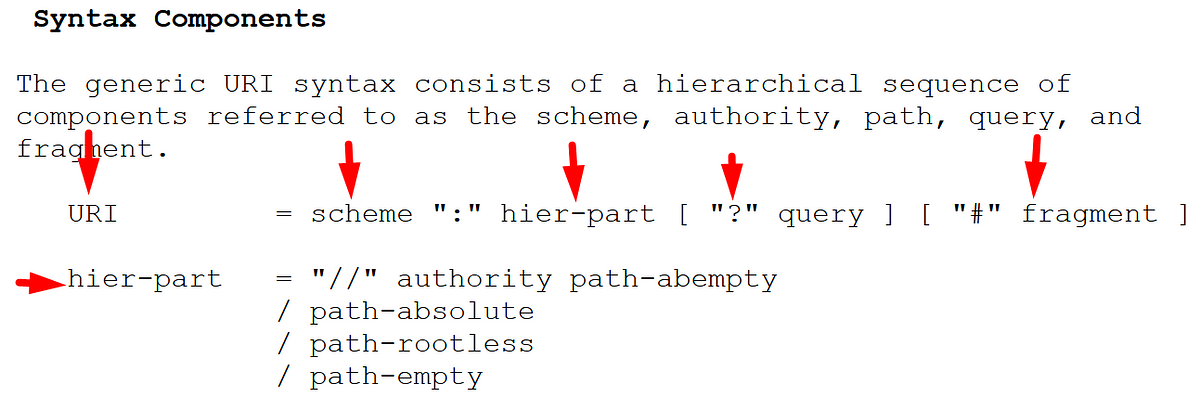
In WebSecurity, APISecurity, Apr 06, 2020A secret note to Bug hunters about URL structure and its parsers.
Understanding the proper URL structure is important to every Bug bounty hunter. So lets go deep dive into the URL structure.
In WebSecurity, Mar 14, 2020owasp
How I perform the JSON CSRF with method override technique.
CSRF(Cross-Site Request Forgery) is a kind of web application vulnerability, using this a malevolent can forge the HTTP request without the actual user knowledge. This will result in ...
In WebSecurity, APISecurity, Dec 29, 2023Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
In WebSecurity, cross-site-scripting, Sep 30, 2023Learn and Earn with the Most Common Unsecured Methods of OTP Bypass Techniques.
Discover the ultimate guide for bug bounty hunters to detect sneaky OTP validation vulnerabilities!
In WebSecurity, APISecurity, Jul 11, 2023The Importance of Checking User-Agent Header Dependency in Penetration Testing.
Never ever give a chance to leave a bug to automated scanners.Introduction:
In WebSecurity, APISecurity, Jun 02, 2023How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022Never leave this tip while you are hunting Broken Access Control.
A special Bug-Bounty tip for Bug hunters and Pen-testers
In WebSecurity, APISecurity, Nov 12, 2021How-to-deploy-a-personal-VPN-in-Linode
A better way to take control of your online privacy
In secureinfrastructure, Jul 11, 2021Genymotion-Xposed-Inspeckage-Setup.
Android application dynamic analysis lab setup on windows
In AndroidSecurity, MobileAppPT, Jul 03, 2021An unknown Linux secret that turned SSRF to OS Command injection.
A weird approach to escalate the Server-Side Request Forgery
In WebSecurity, APISecurity, Mar 17, 2021Let’s know How I have explored the buried secrets in the Xamarin application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Feb 20, 2021Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Jan 18, 2021Hack crypto secrets from heap memory to exploit Android application.
Due to the short time of development, The developers only focus on the building feature, functionalities and UI components. But they may…
In AndroidSecurity, MobileAppPT, Dec 22, 2020Android Hacking Fundamentals -Part-2.
By defalut production build of Android (that’s what you have on your phone until you unlock the bootloader and flash the phone with …
In MobileAppPT, AndroidSecurity, Dec 18, 2020Let’s pen-test make easier with raw0xy.
raw0xy is a python script, takes a file that contains raw HTTP request and a proxy route. Then the script will parse the raw HTTP request…
In WebSecurity, APISecurity, Dec 16, 2020Android Hacking Fundamentals -Part-1.
Before learning about the android application hacking, it is necessary to understand the fundamental concepts of android application files, components and how the different components...
In AndroidSecurity, MobileAppPT, Sep 27, 2020Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020Every Bug Bounty hunter should know the evil smile of the JSONP over the browser’s Same Origin.
JSONP stands for JSON with Padding. It is a JavaScript technique to request the data from the server and can access without worrying about
In WebSecurity, APISecurity, Apr 06, 2020A secret note to Bug hunters about URL structure and its parsers.
Understanding the proper URL structure is important to every Bug bounty hunter. So lets go deep dive into the URL structure.
In WebSecurity, Mar 14, 2020ITSecurity
How I perform the JSON CSRF with method override technique.
CSRF(Cross-Site Request Forgery) is a kind of web application vulnerability, using this a malevolent can forge the HTTP request without the actual user knowledge. This will result in ...
In WebSecurity, APISecurity, Dec 29, 2023The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
In WebSecurity, cross-site-scripting, Sep 30, 2023Learn and Earn with the Most Common Unsecured Methods of OTP Bypass Techniques.
Discover the ultimate guide for bug bounty hunters to detect sneaky OTP validation vulnerabilities!
In WebSecurity, APISecurity, Jul 11, 2023The Importance of Checking User-Agent Header Dependency in Penetration Testing.
Never ever give a chance to leave a bug to automated scanners.Introduction:
In WebSecurity, APISecurity, Jun 02, 2023How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022Never leave this tip while you are hunting Broken Access Control.
A special Bug-Bounty tip for Bug hunters and Pen-testers
In WebSecurity, APISecurity, Nov 12, 2021How-to-deploy-a-personal-VPN-in-Linode
A better way to take control of your online privacy
In secureinfrastructure, Jul 11, 2021Genymotion-Xposed-Inspeckage-Setup.
Android application dynamic analysis lab setup on windows
In AndroidSecurity, MobileAppPT, Jul 03, 2021Let’s know How I have explored the buried secrets in the Xamarin application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Feb 20, 2021Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Jan 18, 2021Hack crypto secrets from heap memory to exploit Android application.
Due to the short time of development, The developers only focus on the building feature, functionalities and UI components. But they may…
In AndroidSecurity, MobileAppPT, Dec 22, 2020Android Hacking Fundamentals -Part-2.
By defalut production build of Android (that’s what you have on your phone until you unlock the bootloader and flash the phone with …
In MobileAppPT, AndroidSecurity, Dec 18, 2020Let’s pen-test make easier with raw0xy.
raw0xy is a python script, takes a file that contains raw HTTP request and a proxy route. Then the script will parse the raw HTTP request…
In WebSecurity, APISecurity, Dec 16, 2020Android Hacking Fundamentals -Part-1.
Before learning about the android application hacking, it is necessary to understand the fundamental concepts of android application files, components and how the different components...
In AndroidSecurity, MobileAppPT, Sep 27, 2020Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020Every Bug Bounty hunter should know the evil smile of the JSONP over the browser’s Same Origin.
JSONP stands for JSON with Padding. It is a JavaScript technique to request the data from the server and can access without worrying about
In WebSecurity, APISecurity, Apr 06, 2020A secret note to Bug hunters about URL structure and its parsers.
Understanding the proper URL structure is important to every Bug bounty hunter. So lets go deep dive into the URL structure.
In WebSecurity, Mar 14, 2020browser-flaw
Every Bug Bounty hunter should know the evil smile of the JSONP over the browser’s Same Origin.
JSONP stands for JSON with Padding. It is a JavaScript technique to request the data from the server and can access without worrying about
In WebSecurity, APISecurity, Apr 06, 2020A secret note to Bug hunters about URL structure and its parsers.
Understanding the proper URL structure is important to every Bug bounty hunter. So lets go deep dive into the URL structure.
In WebSecurity, Mar 14, 2020webbasics
A secret note to Bug hunters about URL structure and its parsers.
Understanding the proper URL structure is important to every Bug bounty hunter. So lets go deep dive into the URL structure.
In WebSecurity, Mar 14, 2020cookie-security
How I perform the JSON CSRF with method override technique.
CSRF(Cross-Site Request Forgery) is a kind of web application vulnerability, using this a malevolent can forge the HTTP request without the actual user knowledge. This will result in ...
In WebSecurity, APISecurity, Dec 29, 2023The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
In WebSecurity, cross-site-scripting, Sep 30, 2023The Importance of Checking User-Agent Header Dependency in Penetration Testing.
Never ever give a chance to leave a bug to automated scanners.Introduction:
In WebSecurity, APISecurity, Jun 02, 2023How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Jan 18, 2021Let’s pen-test make easier with raw0xy.
raw0xy is a python script, takes a file that contains raw HTTP request and a proxy route. Then the script will parse the raw HTTP request…
In WebSecurity, APISecurity, Dec 16, 2020Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020Every Bug Bounty hunter should know the evil smile of the JSONP over the browser’s Same Origin.
JSONP stands for JSON with Padding. It is a JavaScript technique to request the data from the server and can access without worrying about
In WebSecurity, APISecurity, Apr 06, 2020aws
Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020DNS-Security
Weird “Subdomain Take Over” pattern of Amazon S3.
Even though you have an idea on the subdomain takeover via AWS S3. In this write-up, I will show the non-typical way of S3 subdomain
In WebSecurity, CloudSecurity, May 31, 2020android
Genymotion-Xposed-Inspeckage-Setup.
Android application dynamic analysis lab setup on windows
In AndroidSecurity, MobileAppPT, Jul 03, 2021Let’s know How I have explored the buried secrets in the Xamarin application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Feb 20, 2021Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Jan 18, 2021Hack crypto secrets from heap memory to exploit Android application.
Due to the short time of development, The developers only focus on the building feature, functionalities and UI components. But they may…
In AndroidSecurity, MobileAppPT, Dec 22, 2020Android Hacking Fundamentals -Part-2.
By defalut production build of Android (that’s what you have on your phone until you unlock the bootloader and flash the phone with …
In MobileAppPT, AndroidSecurity, Dec 18, 2020Android Hacking Fundamentals -Part-1.
Before learning about the android application hacking, it is necessary to understand the fundamental concepts of android application files, components and how the different components...
In AndroidSecurity, MobileAppPT, Sep 27, 2020reverse-engineering
Hack crypto secrets from heap memory to exploit Android application.
Due to the short time of development, The developers only focus on the building feature, functionalities and UI components. But they may…
In AndroidSecurity, MobileAppPT, Dec 22, 2020ReactNative
Let’s know How I have explored the buried secrets in React Native application.
Mobile Application Penetration Testing Guide
In AndroidSecurity, MobileAppPT, Jan 18, 2021SSRF
An unknown Linux secret that turned SSRF to OS Command injection.
A weird approach to escalate the Server-Side Request Forgery
In WebSecurity, APISecurity, Mar 17, 2021OS-Command-Injection
An unknown Linux secret that turned SSRF to OS Command injection.
A weird approach to escalate the Server-Side Request Forgery
In WebSecurity, APISecurity, Mar 17, 2021VPN
How-to-deploy-a-personal-VPN-in-Linode
A better way to take control of your online privacy
In secureinfrastructure, Jul 11, 2021Broken-Access-Control
Never leave this tip while you are hunting Broken Access Control.
A special Bug-Bounty tip for Bug hunters and Pen-testers
In WebSecurity, APISecurity, Nov 12, 2021dockersecurity
How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022reverseproxy
How to secure-docker-instance-with-basic-Authentication
Nginx reverse proxy with Basic Authentication
In secureinfrastructure, Jul 01, 2022Broken-Authentication
Learn and Earn with the Most Common Unsecured Methods of OTP Bypass Techniques.
Discover the ultimate guide for bug bounty hunters to detect sneaky OTP validation vulnerabilities!
In WebSecurity, APISecurity, Jul 11, 2023Insecure-design
Learn and Earn with the Most Common Unsecured Methods of OTP Bypass Techniques.
Discover the ultimate guide for bug bounty hunters to detect sneaky OTP validation vulnerabilities!
In WebSecurity, APISecurity, Jul 11, 2023waf-bypass
The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
In WebSecurity, cross-site-scripting, Sep 30, 2023XSS
The Art of Identifying X$$ & WAF Bypass Fuzzing Technique.
A smart way to hunt Cross-Site Scripting vulnerability
In WebSecurity, cross-site-scripting, Sep 30, 2023kali-linux
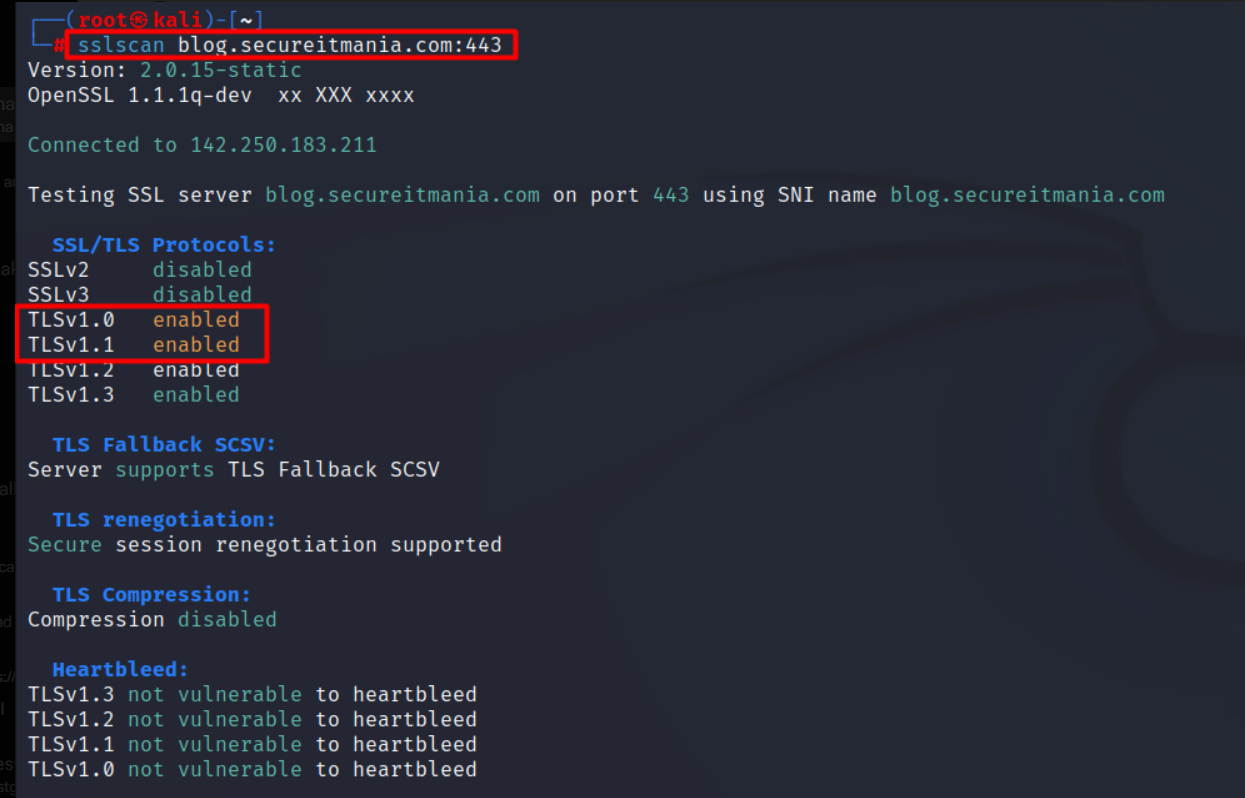
How to analyze the SSL/TLS configuration(sslscan).
SSL/TLS Analysis & Attacks
In network, kali-tool, Dec 28, 2023sslscan
How to analyze the SSL/TLS configuration(sslscan).
SSL/TLS Analysis & Attacks
In network, kali-tool, Dec 28, 2023NTPT
How to analyze the SSL/TLS configuration(sslscan).
SSL/TLS Analysis & Attacks
In network, kali-tool, Dec 28, 2023networksecurity
How to analyze the SSL/TLS configuration(sslscan).
SSL/TLS Analysis & Attacks
In network, kali-tool, Dec 28, 2023xss
Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023injection
Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023websecurity
Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023xss-techinques
Why Appropriate Content-Type Header Matters In REST API Security: Ft. JSON XSS.
Before diving into the specifics of the Content-Type header, let’s quickly recap what REST APIs are all about. REST is an architectural style for designing networked applications. It ...
In APISecurity, XSS, cross-site-scripting, REST-API, Dec 28, 2023